Fake Profiles on LinkedIn & Why You Should be Concerned
If you’re like me, you’ve probably received LinkedIn Invitations from people you don’t know. There are various reasons for accepting LinkedIn invites from strangers. I’ve even read articles about why we should accept LinkedIn invites from folks we don’t know.
Example #1: Forbes, “Why I accept all LinkedIn Contact Requests,” by Dan Schwbel.Example #2: Inc. “What to Do With All Those Random LinkedIn Invites.” In this article John Nemo states, “Put simply, the more people you are connected to on LinkedIn, the more visibility and reach you have on the platform.”
Example #3: The Muse, “4 Valid Reasons You Should Accept Those LinkedIn Requests From Strangers,” by Kat Boogaard. To clarify on Kat Boogaard’s piece, she checks each profile to accepting the invite.
And then there is a fear that this invite is from someone you actually know, but forgot.

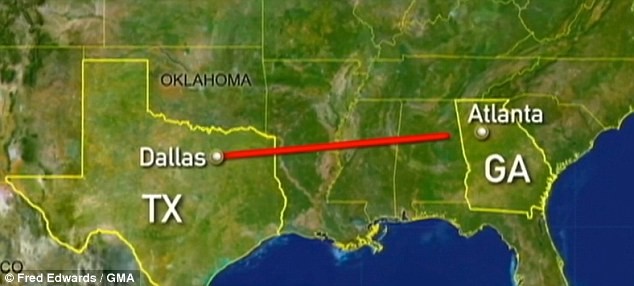
Years ago, LinkedIn would allow the invitee to send a message back to the inviter without first accepting in invitation. I would usually send back a message such as, “Hey, this is really embarrassing for me, but can you remind me which project we worked on together?” 95% of the time, no response. 5% of the time, I would receive strange responses such as, “We met this morning at a networking event in Dallas.” This is funny because I was in Atlanta that day.
Now that I can’t respond to a LinkedIn invite (unless I use inMail), I’m left to making decisions to connect or not to connect on my own.

For any real person who would like to send me a LinkedIn invite, please know that I accept LinkedIn invites from strangers on a regular basis. If we didn’t just chat recently, please include a note saying why you want to connect with me. For example, “Hey I don’t know you, but I wanted to connect with you because I’m looking for a job at your company.” or “Hi, I’ve got a product/service that will solve your problem X and I’d like 15 minutes to pitch my solution.” I appreciate honesty.
In the past few months, I’ve received 4 LinkedIn invitations from profiles that were later removed or deleted shortly thereafter. All profiles had common themes:

#1 giveaway was a stock photo used as the profile picture. Seriously, who has a profile pic on a perfectly white background with 4 co-workers in black/gray suits in the background?
The other common threads that I found a bit odd were:
- First name in ALL CAPS.
- Education was a college with “North” in the school name. (North Florida, North Carolina)
- Very few connections
- Lack of description under each work experience
Here are screenshots from LinkedIn invitations that I received and were subsequently removed from LinkedIn altogether.
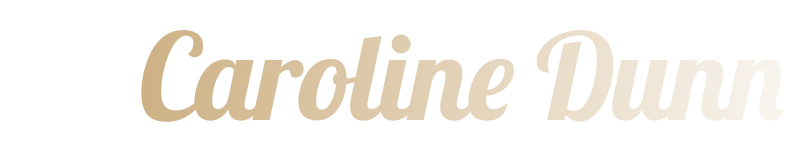
#1 received around April 3rd, 2016
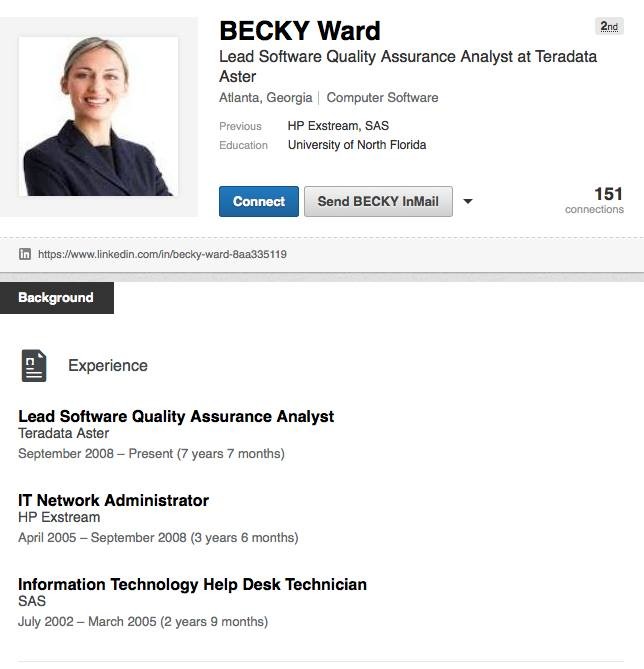
#2 received on April 14, 2016
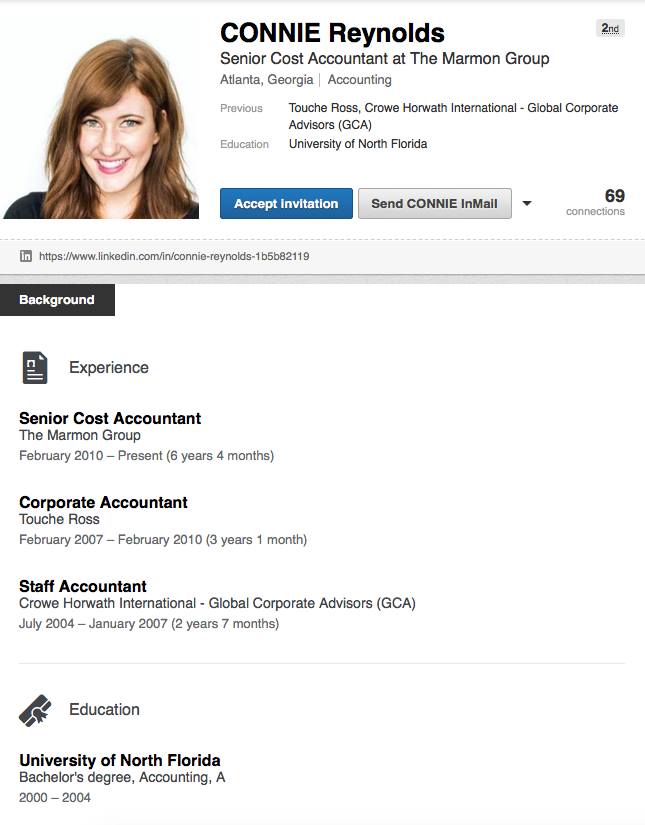
#3 received on May 3, 2016
#4 received on August 12, 2016
This made me wonder why someone would want to connect under a fake profile. What I found was disturbing.
Yahoo Tech reported, “LinkedIn is the perfect entry point for any scammer trying to gain access to your network,” https://www.yahoo.com/tech/how-hackers-are-using-fake-1312602721615926.html
Symantec reported, “…scammers can also scrape contact information from their connections, including personal and professional email addresses as well as phone numbers. This information could be used to send spear-phishing emails.” http://www.symantec.com/connect/blogs/fake-linkedin-accounts-want-add-you-their-professional-network
Here’s an article with a very specific method to spot a fake LinkedIn profile – http://www.ignitesocialmedia.com/linkedin-marketing/avoid-being-catfished-how-to-spot-a-fake-linkedin-profile-with-one-click/
With the hackers getting more sophisticated and the # of connected devices exploding, we need to be even more vigilant about protecting our privacy and security. I’ve been told at least a thousand times not to click on links in emails from strangers, or and any email that seems “fishy” from a friend. I know better than to provide sensitive information on a web form. Unless I talked to you last week, AND you look like your LinkedIn profile pic, I read every LinkedIn profile prior to accepting in the invite.
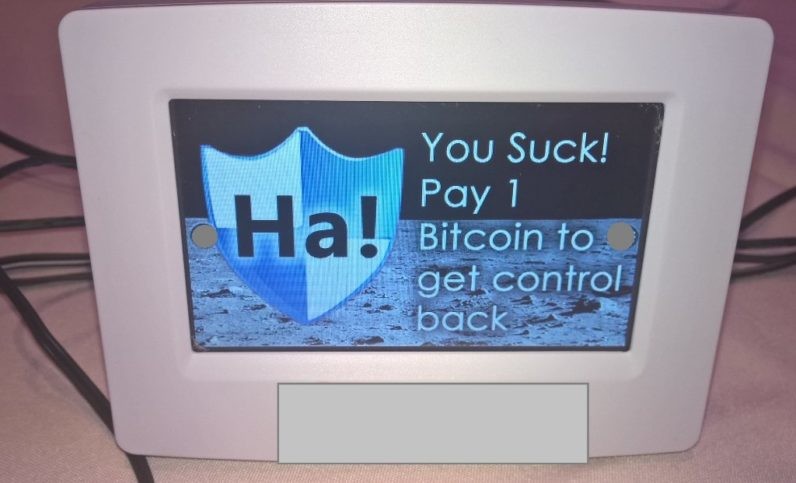
Worst Case Scenario: Your LinkedIn hacker gets control of your home automation network, locking you out from your thermostat and demands 1 bitcoin to allow you to change the temperature in your own home.
This brings me to my next blog post on security for connected devices / IoT. Next week, I’ll post my takeaways from the Wireless Technology Forum’s Cyber Security Panel including security experts from Predikto, NexDefense, & WanderingWiFi.