3 Key Learnings from the Wireless Forum’s CyberSecurity Panel
3 common scenarios of cyber crimes from the experts, and creating a cybersecurity action plan.
The panel discussion at the Wireless Technology Forum took a turn for the serious during the Ransomware and CyberSecurity session on August 17, 2017. The Wireless Technology Forum assembled a team of diverse CyberSecurity experts including panelists from the DOJ, Barnes and Thornburg, LLP law firm, and 2 independent privacy consultants. Three key trends in cybersecurity emerged from the panel discussion.

#1 – Social Engineering
Assistant United States Attorney, Samir Kaushal named social engineering as the top cyber crime that comes across his desk. Specifically wire transfer fraud.
The most common scam is receiving an urgent request from your boss to wire money into an account. AUSA Kaushal described how victims would receive an email that appeared to be from their boss with an additional character such as an ‘i’ in the email address. The employee would believe they were corresponding with their boss directly and urgently needed a wire transfer. In one such case, AUSA Kaushal was able to stop a transfer of $700,000 from a university since the university reported the crime to the DOJ and FBI. He urged everyone to report any and all cybercrimes.
Check out this warning from the FBI published by Fortune on May 5, 2017.
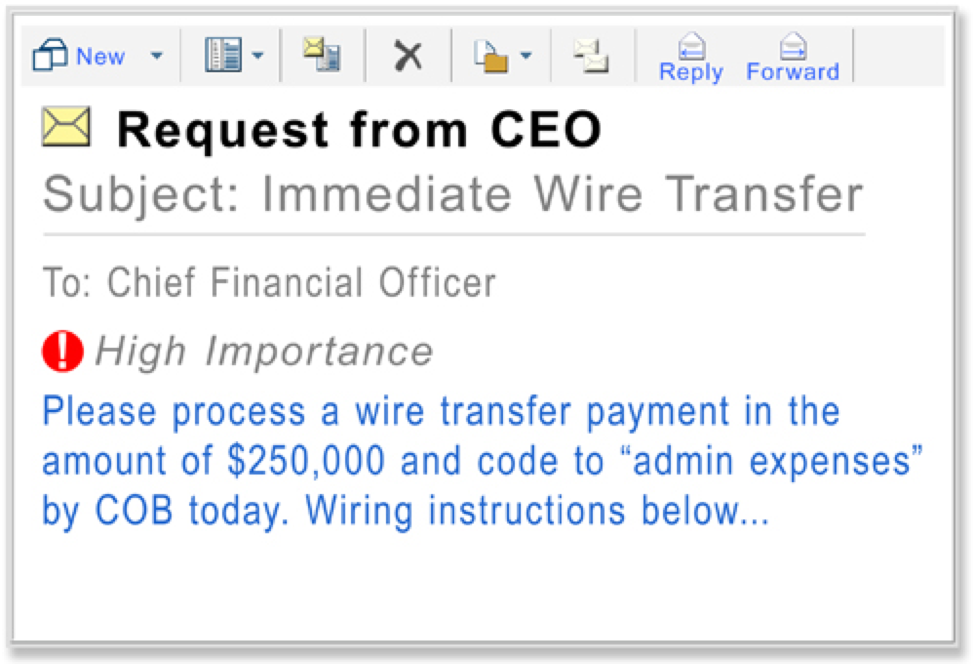
Credit: FBI
Keith Coleman, Founder & CEO, fraudmarc, quantified the problem at $5 Billion in the past year.
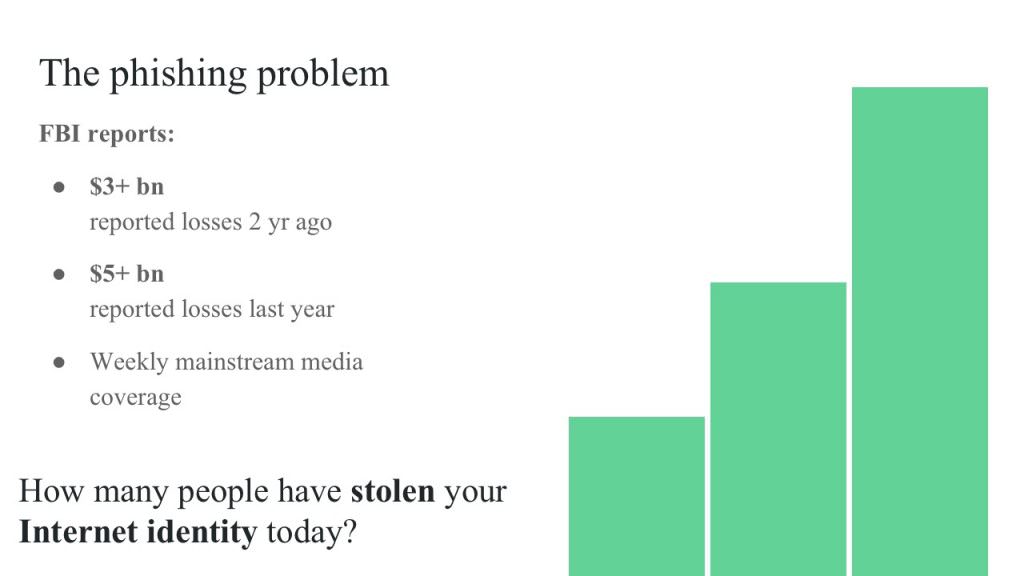
Credit: fraudmarc, August 2017 Top Innovator, Wireless Technology Forum (slide 12)
#2 – Intersection of Privacy and Security
Jodi Daniels, Red Clover Advisors, explained that advertisers have become more sophisticated in targeting people instead of just devices. If you provide your personal information to company A for a free app, Company A could sell your information to Company B, C, D, E, and F. For example, Unroll Me was a free service that promised to unsubscribe users from email lists, but Unroll Me used their access to email inboxes to scrape for competitive information and sold that information. In my own research, Unroll Me allegedly scraped emails for Lyft information and sold that information to Uber.
#3 Ransomware
Ransomware has surged in recent years. How much? CNN Tech reported $209 million was extorted by cyber-criminals in the first quarter of 2016. And that dollar amount could be significantly lower than the real number as most companies don’t report cyber crimes for fear of bad PR.
AUSA Kaushal once again urged the audience to report all cyber crimes to the DOJ and FBI. The information gathered during the investigation is used to prosecute the cyber criminal, not the company or its employees.

Your CyberSecurity Action Plan
Prevention
Karun Rajasekharan, Meru Consulting, helps small to medium sized companies comply with vendor SLAs. One of his clients bootstrapped their initial product; and after signing a large service provider contract, they realized they had to re-architect their entire product to comply with client’s data storage requirements.
Not all privacy compliance issues are quite as drastic.
Where to Start?
The panel advised companies to start with a GDPR Assessment. Companies should take an inventory of their data, map it out, and understand use of data.
Jason Bernstein, Partner, Intellectual Property Group, Barnes and Thornburg, LLP went as far as to advise the audience to not accept or mask unnecessary data as a vendor.

Reaction
You’ve been hacked.
- Contact the FBI and report the crime.
- Work with your legal and IT teams to resolve the issue as quickly as possible.
- Contact your affected customers and provide an assessment of the compromise, resolution, and timeline.
It is only through working with the DOJ and FBI, can cyber criminals be brought to justice.
There were additional important points discussed regarding handling security vulnerabilities and European privacy laws that I failed to include for the sake of brevity.
Watch the entire panel discussion via the Wireless Forum’s YouTube channel here: